LastPass → 1Password migration
Just three days ago, the news broke that LastPass’s security incident this summer involved leaking the complete — but encrypted — vaults of all their customers, including unencrypted information about who the customers are. And, since I’ve been a customer of LastPass for a long time, I have over 600 passwords stored in the service.
Poor communication
To make matters worse, their communication in regards to this have been unclear. This is the e-mail I received:
Note that the e-mail (titled “Update on Recent Security Incident”) does not mention at all the severity of what was leaked. In the linked blog post, you have to read through 4 paragraphs to get to the part about actual vaults being leaked. This poor communication lead to me initially missing the fact that my vault had been leaked; the first paragraphs downplays everything that had happened up to that point.
Poor security
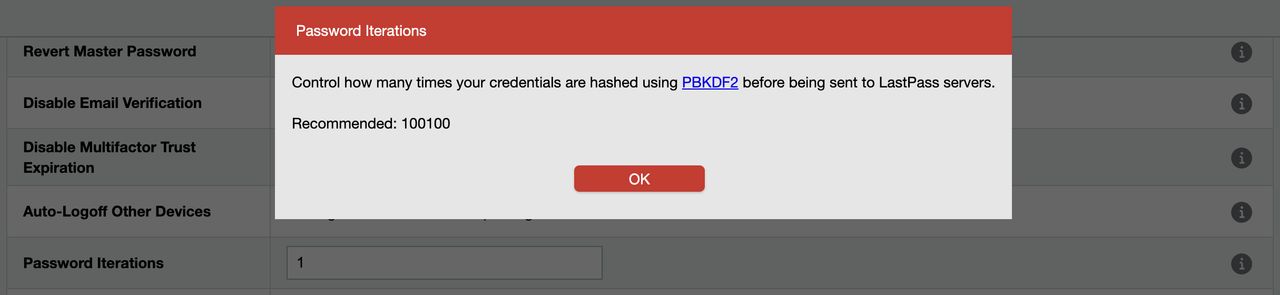
I am extra concerned about my account, since it appears from discussions online that the whole issue is around how many iterations of PBKDF2 are applied. My account with Lastpass is pretty old (from 2011), and from discussions online people are reporting that 5000 iterations was the case a while back, but 100 100 is the default now. Checking my account I find that my account apparently has only 1 iteration of PBKDF2 (see the “Password iterations” field in the background)!
The alternative
I quickly decided that moving away from LastPass was the right way forward; they have demonstrated a lack of integrity in their handling of this very serious incident, and are no longer deserving of my trust. This meant that I would have to move a vault of 600 passwords across to a different service.
Reading for a little while, it becomes quite clear that 1Password is the alternative to look to, and so far I haven’t been disappointed. First of all, the native Mac app is really good (I haven’t gotten around to Windows yet, as I am on vacation). Second, it builds in the TOTP generation, so it is available both on my computer and on my phone.
Migration process
- Export LastPass vault unencrypted, and import it into 1Password. Good guide from 1Password. Done!
- Change passwords of most important accounts (never giving the new passwords into LastPass). Done!
- Add 2FA to accounts I deem important in the walk-through, and move all other 2FA to 1Password.
- Delete LastPass account.
- Systematically change passwords of less important accounts over time.
Some notes
- This is a good time to select a longer passphrase instead of a master password.
- After importing my vault, I tagged all of my entries with a tag (”Review2023”). I did that by editing one item, and adding that tag. Then I selected all of entries, and dragged them into the tag on the left-hand side; which tagged all of them at once. I now remove this tag whenever I change the password for an entry.
- You can use 1Password as an
ssh-agent, which can drastically simplify my workflow. I haven’t had a chance to try this out yet, and I am excited to figure out how this works on Windows with WSL. - The 1Password CLI looks interesting.
